This guide outlines how PKI public key infrastructures operate to provide optimum cyber security.
According to the Internet Data Cooperation (IDC), there will likely be 42 billion IP-connected devices by 2025. However, they will all need to be protected. Millions of organizations have therefore built their cybersecurity on public-key infrastructures (PKIs) in recent years, securing and encrypting communications between two devices.
How do PKI public key infrastructures work?
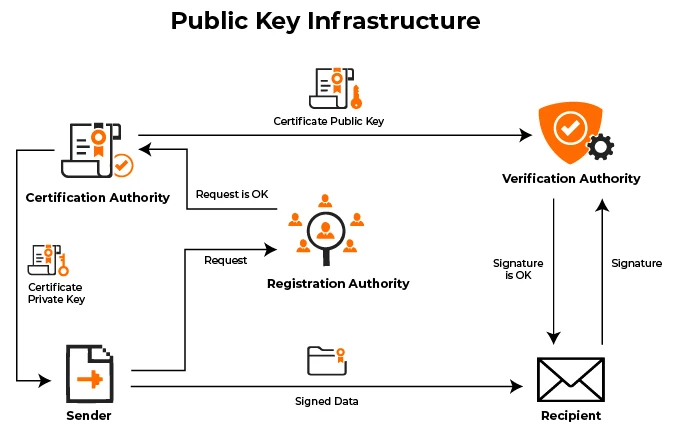
PKIs are based on two keys: a public public key and a private private key. After ensuring the identity of the key holder, the system issues such a key pair. The public key is used by the sender, i.e. the cloud or website, to encrypt a message. This message can only be decrypted with the recipient’s specific private key.
A PKI is always structured as a multi-level security pyramid in which the root certificate authority (CA) authorizes the issuing CAs. The cryptographic keys are generated for the end devices and users after successful confirmation.
SaaS or cloud
In order to secure devices and also services, such as vulnerability management, many device manufacturers are engaged in designing public key infrastructures. Many companies now have to decide whether to obtain a PKI using the SaaS model or via a cloud platform.
In the SaaS model, for an enterprise to arrive at the appropriate PKI from the cloud, it should first specify and conceptualize the entire PKI. This includes the creation of security policies, according to which the necessary system environments are defined as part of the conception. This also includes operating concepts which, among other things, take load analyses, availability requirements and geo-concepts into account. A decision-making basis for the further operating model can be derived from these findings. A decision must be made as to whether the company needs a PKIaaS, goes to the cloud or prefers to remain in its own data center.
If a company mainly wants to implement standard use cases with its public key infrastructure that require little customization, a PKIaaS is a good choice for issuing the standard certificates for servers, TLS (Transport Layer Security) or the VPN. The implementation is simple, fast, inexpensive, is ready for use immediately afterwards, and is billed either per certificate or per device.
However, if an extensive implementation or a very specific use case is on the horizon, a cloud platform comes into focus. Special cases, such as certificates not based on the TSL protocol, can also be mapped via API access. Often, DevOps teams that need to integrate a PKI layer into a product benefit from this option.
The IT team keeps track of all public key infrastructure components such as CA, Registration Authority (RA) and Validation Authority (VA) via the cloud console with the Certificate Revocation List (CRL) and Online Certificate Status Protocol (OCSP). It can also map and control on-premises PKI functionality in a cloud platform. It can even add a hardware security module (HSM) in the cloud as a service.
PKI – On Premises
However, the cloud does not make on-premises implementations obsolete. On-premises PKI should not be ruled out immediately because of this. The question is whether an infrastructure is capable of handling all incoming requests at any given time. Many e-commerce merchants require significantly higher capacities at short notice than would otherwise be the case. With on-premises, a large part of the resources would lie idle for the rest of the year, should the company need to keep them permanently. However, if the volume of requests in the use case remains consistent and the necessary expertise is available within the company’s own organization, then on-premises implementation could remain an attractive option.
The best option of on-premises, cloud platform and PKI-as-a-Service must therefore be weighed up individually in each case.
ALSO READ: How to use a VPN setup to protect your security against hacks and snooping




